OWASP ZAP / Zaproxy¶
Zaproxy is a widely used, open source security testing tool. It is intended to be used by those new to application security as well as professional penetration testers.
- Download: https://www.zaproxy.org/
- Documentation: https://github.com/zaproxy/zaproxy/wiki
We specifically support the Zaproxy output!
Learn by example
Check out our example Zaproxy repository.
Set up Zaproxy in Gitlab¶
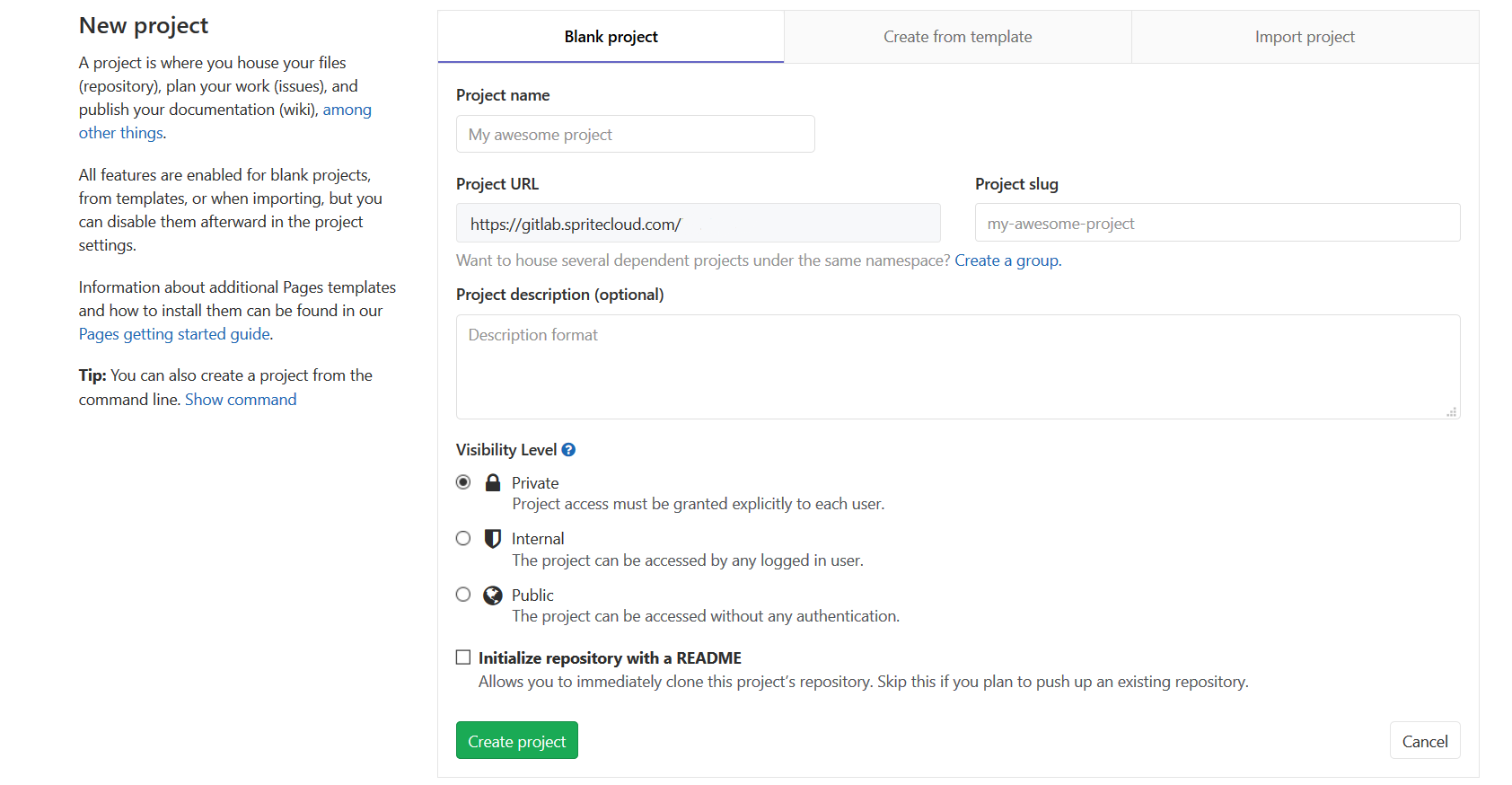
- To set up a Zaproxy CI in Gitlab you will need a Gitlab account and a Gitlab project.
-
You will also need a Gitlab personal access token.
- You can create your access token by clicking on your avatar in the upper-right corner and select Settings
- Click on Access Tokens in the left menu
- Choose a name and optional expiry date for the token
- For scope select API
- Click the Create personal access token button
- Once you leave or refresh the page, you won’t be able to see your token again so copy it somewhere save
-
To push your result to Calliope you will need an account on Calliope.pro too.
-
Create a new .gitlab-ci.yml file in the root of your project, copy the example gitlab job from below and update the following with your own values:
HOME_URL (the website you want to have scanned)
API_KEY (your Calliope API key)
PROFILE_ID (the Calliope profile ID)
-
Save the .gitlab-ci file and start a testrun
- Link the Calliope group with the gitlab job (see: Calliope GitLab Integration )
Example¶
run-security-test:
image: owasp/zap2docker-stable
variables:
HOME_URL: "https://www.calliope.pro"
API_KEY: YOUR_API_KEY
PROFILE_ID: YOUR_PROFILE_ID
allow_failure: true
script:
- mkdir /zap/wrk/
- /zap/zap-baseline.py -x security-report.xml -t $HOME_URL || true
- cp /zap/wrk/security-report.xml .
- curl -X POST -H "x-api-key:$API_KEY" -H "Content-Type:multipart/form-data" -F "file[]=@path/to/testresult" https://app.calliope.pro/api/v2/profile/$PROFILE_ID/import/zaproxy
artifacts:
paths: [security-report.xml]
when: manual
Improve this documentation¶
Do have more information on setting up Zaproxy or how to put it in a different pipeline like Jenkins or Travic CI? Let us know!